All camera lenses have a minimum focusing distance. That is the closest you can be to a subject and still get it in focus.
The minimum focusing distances for iPhone cameras aren’t listed on the tech specs page, but it looks like it’s around four feet on the 5x camera on iPhone 15 Pro Max.
On any traditional camera system, as you move too close it would fail to lock focus and the subject would become blurry. But if you move too close with your iPhone, it will automatically switch to a 5x digital zoom taken from the main camera.
This is because the 1x lens has a much closer minimum focusing distance. This behavior is similar to how recent iPhones switch from 1x to the 0.5x camera for macro shots.
From one point of view this is good because you still get a photo where the subject is in focus. But it will also have visibly reduced quality.
When I tap the 5x button I want to use the 5x camera. That’s why I bought the bigger phone this year. If I know I’m getting the digital zoom I’d rather back up a few inches to get the real thing, but there’s no on-screen indicator that it changed. No icon or text anyway.
If you’re paying attention you can sort of tell when it switches. The cameras are in different positions on the back of your phone, so the image changes perspective ever so slightly. It looks like the image shifted up/down or left/right by a few pixels, which is easy to miss.
If this matters to you, I’d suggest taking some test shots of moderately close subjects to get acquainted with the distance where it transitions between cameras.
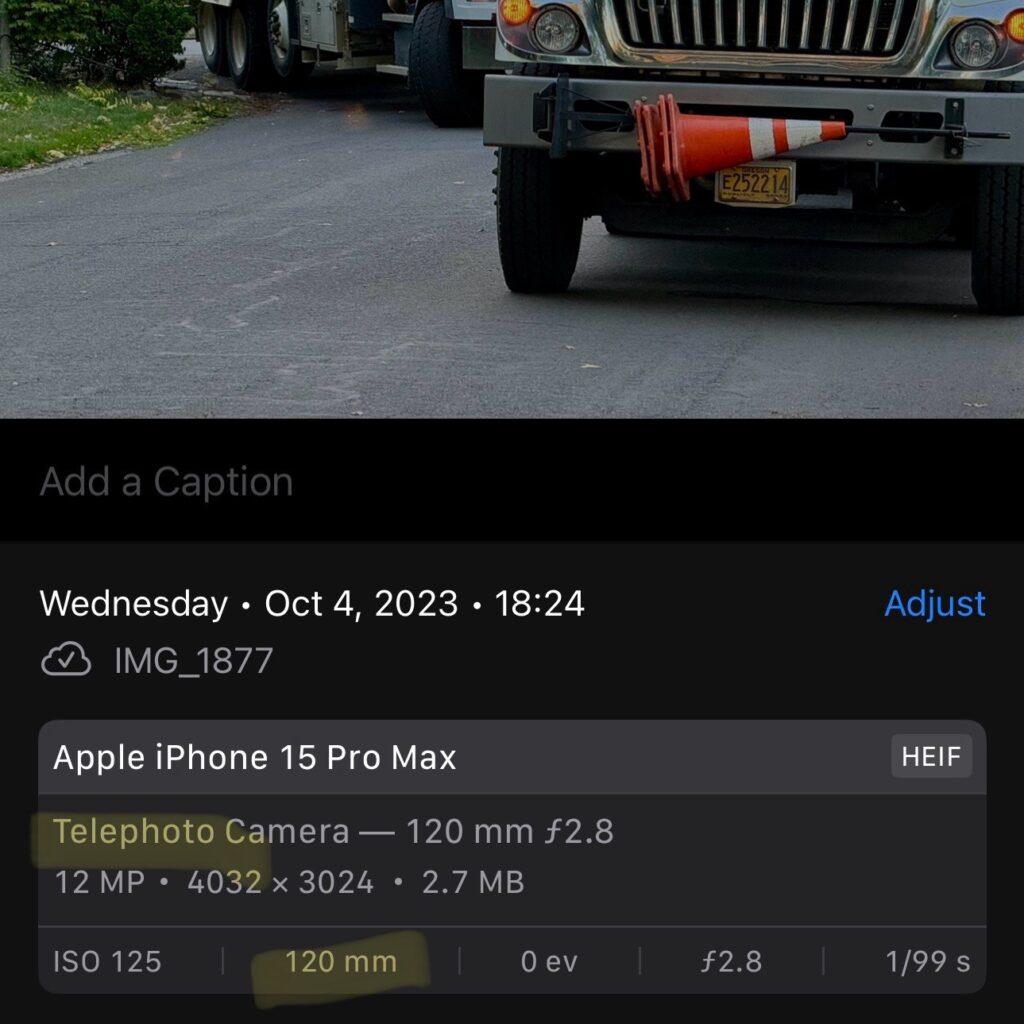
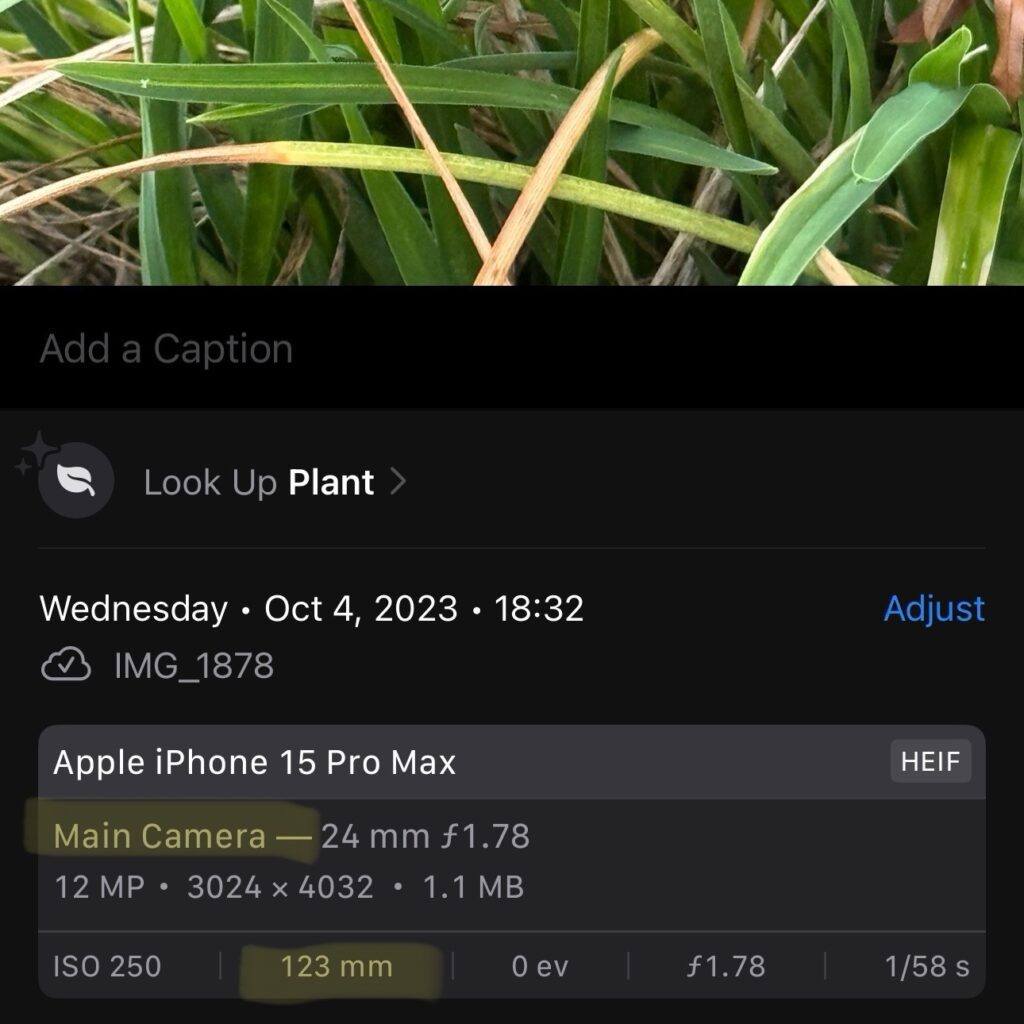
Once you’ve taken some test shots you can swipe up to show their metadata. Look for text that says Telephoto Camera vs. Main Camera. And if you pixel-peep you can definitely tell the difference.
In the examples below you can see the trucks were captured with the telephoto camera while the plant was too close and switched over to a digital zoom on the main camera.